A Bug in Openssl package which let the attacker sniff chunks of data in memory during an SSL communication has caused a worldwide panic. It is due to a missing bounds check in the handling of the Transport Layer Security (TLS) heartbeat extension.
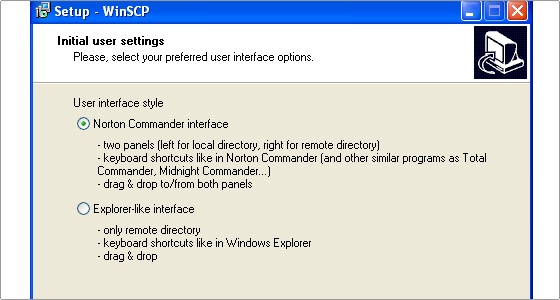
An attacker could exploit this vulnerability by implementing a malicious TLS or Datagram Transport Layer Security (DTLS) client, if trying to exploit the vulnerability on an affected server, or a malicious TLS or DTLS server, if trying to exploit the vulnerability on an affected client.
Devices affected by it are the endpoints which can be either Server or Client . Patch version 1.0.1g has been released to fix the vulnerability and many corporates , banks , govt. organization etc are in a mad rush to patch it.